Critical Infrastructure Security , Cybercrime , Fraud Management & Cybercrime
FBI: DarkSide Ransomware Used in Colonial Pipeline Attack
Company Moves Into Remediation Phase; White House Monitoring Incident
The FBI and the White House confirmed Monday that the DarkSide ransomware variant was used in the Friday attack that caused disruptions at Colonial Pipeline Co., which operates a 5,500-mile pipeline that supplies fuel, gasoline and other petroleum products throughout large portions of the eastern U.S.
See Also: The Auto Industry’s Quick Guide to Regulations & Compliance
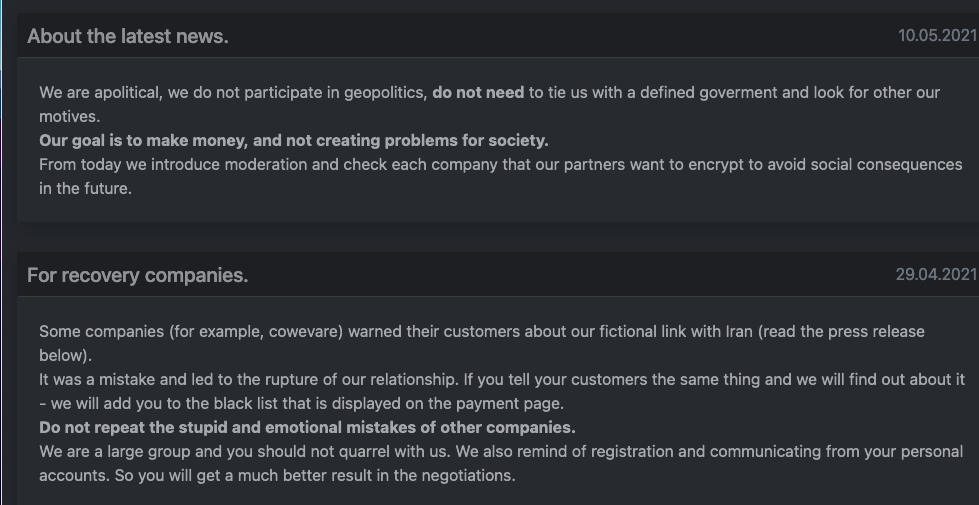
The cybercriminal group behind DarkSide ransomware, however, appeared to try to shift the blame for the incident to an affiliated organization in a posting on its darknet website.
Speaking at the White House on Monday, President Joe Biden noted: "The Federal Bureau of Investigation has determined Colonial’s network was infected by ransomware, and it’s a criminal act, obviously. The FBI released details of the attack so others can take steps to prevent being infected. My administration ... takes this very seriously. We have efforts underway with the FBI and [Department of Justice] - to disrupt and - and prosecute ransomware criminals. And my administration will be pursuing a global effort of ransomware attacks by transnational criminals who often use global money-laundering networks to carry them out."
Gregory Touhill, a retired U.S. Air Force general who is now director of the Carnegie Mellon University Software Engineering Institute's CERT Division, notes that the Colonial Pipeline attack could be the start of a trend toward attackers focusing on critical infrastructure providers to either gain hefty ransoms or disrupt the economy.
"This could just be the start of a global campaign against critical infrastructure that could adversely affect populations around the world," Touhill says.
FBI Update
In a Monday statement, the FBI confirmed that "the DarkSide ransomware is responsible for the compromise of the Colonial Pipeline networks. We continue to work with the company and our government partners on the investigation."
The FBI did not say who waged the attack on Colonial Pipeline, but the ransomware is most closely associated with its creators - the DarkSide gang - according to the security firms Cybereason and Secureworks.
The DarkSide gang, however, appeared to claim that an affiliate was responsible for the attack that forced the energy company to stop the flow of fuel through its pipelines over the weekend.
"Our goal is to make money, and not creating problems for society. From today we introduce moderation and check each company that our partners want to encrypt to avoid social consequences in the future," according to a note posted to the DarkSide gang's darknet website on Monday, Emsisoft reports.
While the FBI, the Cybersecurity and Infrastructure Security Agency and security firms continued to investigate the attack, Colonial Pipeline posted an update Monday, saying that it's working to incrementally bring IT systems and portions of its pipeline back online. The company's goal is to "substantially" restore service by the end of this week.
"While this situation remains fluid and continues to evolve, the Colonial operations team is executing a plan that involves an incremental process that will facilitate a return to service in a phased approach," according to the company update. "This plan is based on a number of factors, with safety and compliance driving our operational decisions and the goal of substantially restoring operational service by the end of the week. The company will provide updates as restoration efforts progress."
At a White House briefing Monday, Anne Neuberger, the deputy national security adviser for cyber and emerging technology, noted that Colonial Pipeline is in the remediation phase and is working with a security firm - reportedly FireEye Mandiant - to resolve the issue. While the government is providing support, the company is addressing the recovery itself, Neuberger added.
Colonial Pipeline first acknowledged the ransomware attack against its systems on Saturday after the company shut down its operations on Friday. The Georgia-based company connects refineries in the Gulf Coast to customers throughout the southern and eastern U.S. through a pipeline system of more than 5,500 miles. This pipeline carries gasoline, diesel, jet fuel and home heating oil as well as fuel for the military.
Colonial Pipeline transports about 45% of all the fuel consumed on the East Coast and serves almost 50 million U.S. customers, the company notes.
Impact on Fuel Supply
In response to concerns about potential increases in gas prices and possible fuel shortages, the Federal Motor Carrier Safety Administration issued a regional emergency declaration that allows transport drivers stretching from the South through the Northeast to work more hours through June 8. It applies to 17 states and the District of Columbia (see: Colonial Pipeline Starts Recovery From Ransomware).
Deputy National Security Adviser Elizabeth Sherwood-Randall, speaking at the White House briefing, noted that the U.S. Department of Energy has been in contact with state and local organizations to address any fuel shortage issues. And while there is currently no fuel shortage tied to the pipeline shutdown, the government is preparing for such a shortage.
Neuberger noted that Colonial Pipeline decided to shut down parts of its systems Friday to ensure that the ransomware did not spread to the company's operational technology systems and further damage the pipeline and industrial control systems that control it.
Like the president, Neuberger categorized the attack on the pipeline company as a "criminal" act, but she said there's no indication that a nation-state is associated either with the attack or the ransomware group behind it. She added that the U.S. intelligence community, however, is monitoring the situation.
"It’s doubtful that DarkSide would work alongside a nation-state for this attack," says Fleming Shi, CTO of Barracuda Networks. "DarkSide is a 'cyber weapon software provider' to hackers, and a nation-state could well weaponize it. But I don’t think DarkSide is interested in partnering with a particular nation, putting a giant target on themselves."
Neuberger did not comment on whether the attackers who targeted Colonial Pipeline had contacted the company or whether the firm is negotiating over a possible ransom payment.
And while the FBI has noted in the past that it discourages companies and individuals from paying ransomware gangs, Neuberger said that decisions are ultimately left to the organization that has been targeted.
"We recognize, though, that companies are often in a difficult position if their data is encrypted and they do not have backups and cannot recover the data," Neuberger said. "And that is why - given the rise in ransomware and given the troubling trend of [attackers] targeting companies that have insurance - we need to look thoughtfully at this area, including with our international partners, to determine what we do in addition to actively disrupting infrastructure and holding perpetrators accountable to ensure that we're not encouraging the rise of ransom."
Insights on DarkSide Gang
Brett Callow, a threat analyst at Emsisoft, says that the DarkSide group may, indeed, be displeased that one of its affiliates may have placed the gang in the spotlight.
"DarkSide may well feel that such a high-profile attack will bring unwanted attention to - and, perhaps, action against - their operations. And other groups may feel the exact same way," Callow says. "Hopefully, they're right. Until now, governments have lacked a clear and decisive strategy to the ransomware problem, and that needs to change or we'll invariably see more and more attacks like this."
The security company Cybereason says the DarkSide gang is a relative newcomer, having been detected in August 2020. The gang primarily strikes targets in English-speaking countries and appears to avoid targets in countries associated with former Soviet Bloc nations, Cybereason notes.
The gang's ransom demands range from $200,000 to $2 million. It reportedly has a "code of conduct" that prohibits attacks against hospitals, hospices, schools, universities, nonprofit organizations and government agencies, Cybereason says.
Sam Curry, the CSO at Cybereason, notes that the DarkSide gang and its affiliates use both phishing emails and vulnerability exploits to start their attacks. Once the attackers gain a foothold, "they spread … patiently, quietly and persistently through a network. They tend to target and move toward domain controllers as a major source of control and operational effectiveness."
Secureworks, which has also tracked DarkSide, labeling it "Gold Waterfall," says the gang has launched 81 "name and shame" extortion-style attacks globally since August 2020.
Critical Infrastructure Under Siege
The attack against Colonial Pipeline has again put the focus on protecting U.S. critical infrastructure and addressing vulnerabilities
In February, attackers targeted the water treatment facility in Oldsmar, Florida (see: Water Treatment Hack Prompts Warning From CISA).
Austin Berglas, who formerly was an assistant special agent in charge of cyber investigations at the FBI's New York office, notes that government agencies have issued numerous reports about cyberthreats to the oil and gas industry for years, and the Colonial Pipeline incident shows that not enough has been done to mitigate risks.
"These attacks are highlighting … that U.S. critical infrastructure lacks the appropriate resources to sufficiently monitor systems, respond appropriately and is using outdated technology not built with appropriate security," says Berglas, who is now global head of professional services at cybersecurity firm BlueVoyant.